Introduction
A new Linux vulnerability is making waves for one simple reason:
It turns a normal user into root… in seconds.
No exploit chain.
No race condition.
No memory leak.
Just a few syscalls.
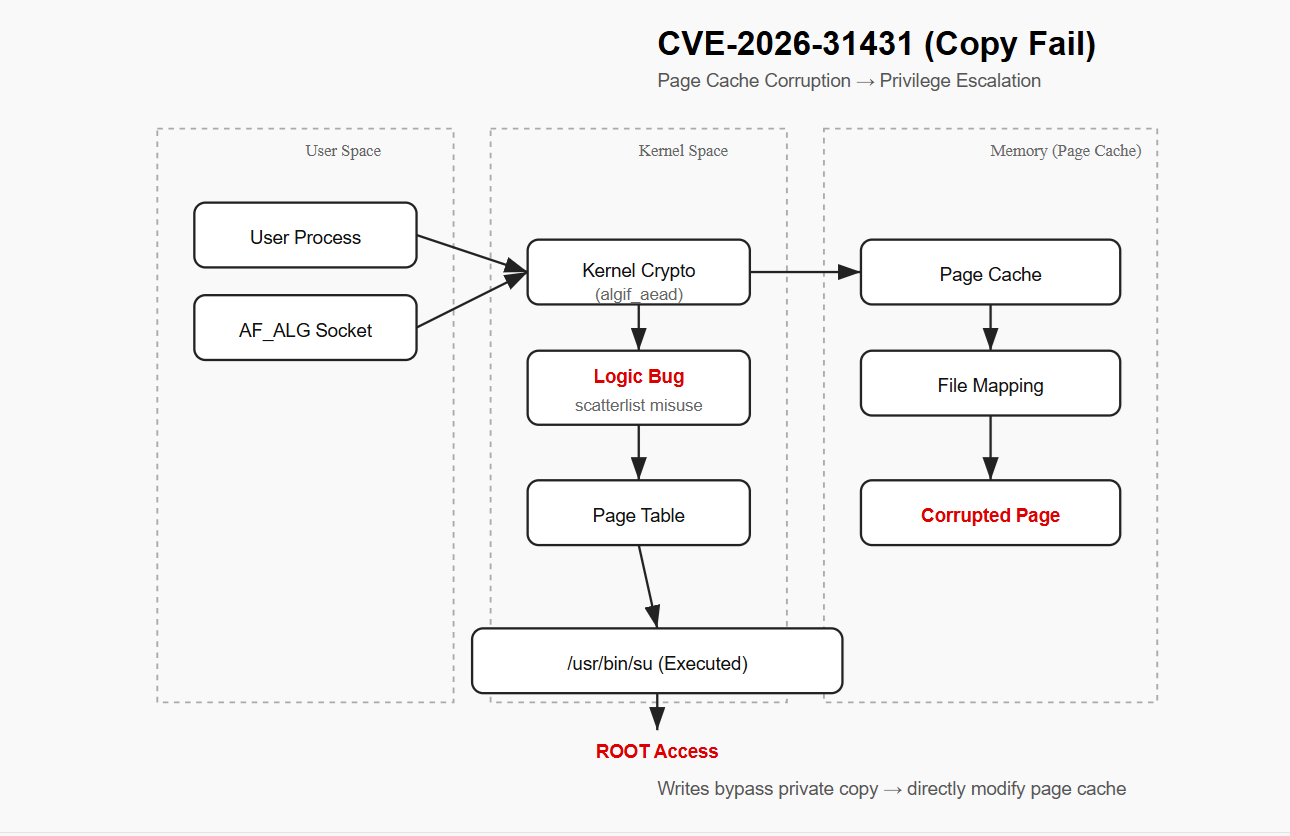
This is CVE-2026-31431, also known as “Copy Fail” — a vulnerability that breaks one of the most fundamental assumptions in Linux:
👉 That files only change when you write to disk.
What Makes This Vulnerability Different?
Most privilege escalation bugs rely on:
- Buffer overflows
- Use-after-free
- Complex timing conditions
This one doesn’t.
Instead, it’s a logic bug in the Linux kernel’s crypto interface:
👉 AF_ALG (algorithm socket interface)
And that difference is everything.
The Core Idea (This Is the Trick)
The attack does NOT modify files on disk.
Instead:
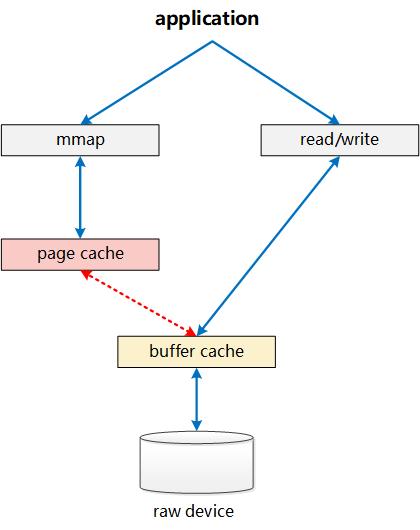
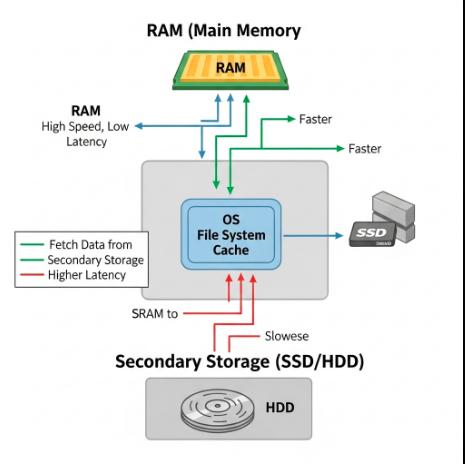
It modifies the page cache — the in-memory representation of files.
👉 Think of it like this:
- Disk file = the “official version”
- Page cache = the working copy in memory
This vulnerability attacks the working copy.
The Attack Path
Let’s walk through it step by step:
1. Entry Point: AF_ALG
The attacker creates a special socket:
socket(AF_ALG, ...)
This interface lets user space access kernel cryptographic operations.
2. Trigger the Bug
Through a combination of:
sendmsg()splice()
The attacker hits a flaw in the kernel:
👉 incorrect in-place scatterlist handling
3. Memory Corruption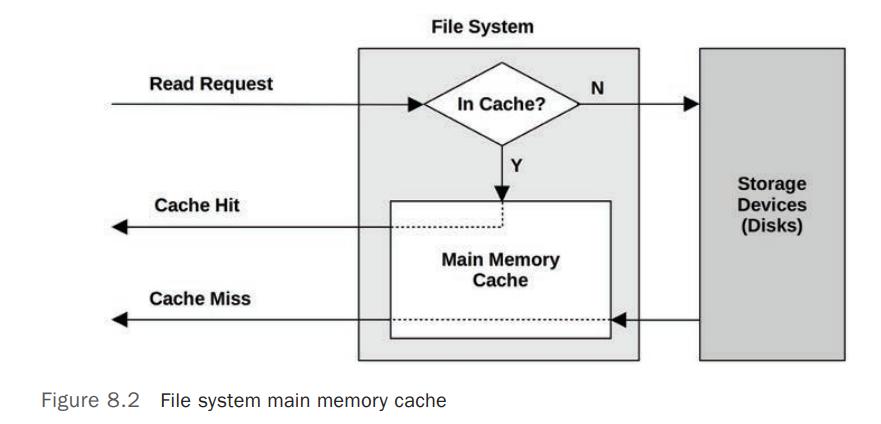
The kernel believes it is writing to a safe buffer.
It’s not.
Instead:
👉 It writes into unintended memory pages
4. Page Cache Pollution
Those pages happen to belong to:
👉 cached system binaries (e.g., /usr/bin/su)
5. Controlled Writes
The attacker can write:
👉 ~4 bytes at a time
Repeatedly.
This allows:
- Precise payload construction
- Shellcode injection
6. Execution
Finally:
/usr/bin/su
But now:
👉 It runs modified code (from memory)
👑 Result
🎯 Root access
⚠️ Why This Is Dangerous
This vulnerability is particularly severe because:
✔ No Disk Changes
- File integrity tools won’t detect it
✔ Highly Reliable
- No race conditions
- Deterministic behavior
✔ Low Privilege Required
- Any local user can exploit it
✔ Works Across Distros
- Affects kernels going back years
🧠 Why This Bug Exists
This vulnerability originates from:
👉 A performance optimization (2017)
The kernel tried to avoid copying memory by using:
“in-place operations”
But:
❌ The memory boundaries were not correctly enforced
🧩 The Real Lesson
This is not just a bug.
It’s a design failure.
The system assumed memory operations were safe…
when they weren’t.
🧠 One Line Summary
This exploit doesn’t change files.
It changes reality.
🛠️ Mitigation
- Update your kernel immediately
- Apply vendor patches
- Restrict local user access where possible
🚀 Closing Thought
Most people think hacking is about breaking things.
This exploit shows something deeper:
Sometimes, you don’t break the system.
You simply convince it… nothing is wrong.