Nmap (“Network Mapper”) is a free and open source utility for network discovery and security auditing. Many systems and network administrators also find it useful for tasks such as network inventory, managing service upgrade schedules, and monitoring host or service uptime. Nmap uses raw IP packets in novel ways to determine what hosts are available on the network, what services (application name and version) those hosts are offering, what operating systems (and OS versions) they are running, what type of packet filters/firewalls are in use, and dozens of other characteristics. It was designed to rapidly scan large networks, but works fine against single hosts. Nmap runs on all major computer operating systems, and official binary packages are available for Linux, Windows, and Mac OS X. In addition to the classic command-line Nmap executable, the Nmap suite includes an advanced GUI and results viewer (Zenmap), a flexible data transfer, redirection, and debugging tool (Ncat), a utility for comparing scan results (Ndiff), and a packet generation and response analysis tool (Nping).
Nmap, short for “Network Mapper,” is a powerful and widely used open-source tool designed for network discovery and security auditing. It is used to scan networks and systems to gather information about the devices connected to the network, identify open ports, services running on those ports, and detect vulnerabilities.
Key Features and Uses of Nmap:
- Network Discovery: Nmap can identify devices on a network, revealing IP addresses, hostnames, and other essential details.
- Port Scanning: Nmap scans for open ports on a target device, helping to identify services and applications running on those ports.
- Service and Version Detection: Nmap can determine the software and version running on open ports, which is useful for vulnerability assessment.
- Operating System Detection: By analyzing network responses, Nmap can guess the operating system and its version running on a target device.
- Vulnerability Detection: With Nmap scripts (Nmap Scripting Engine – NSE), it can detect specific vulnerabilities and misconfigurations.
- Security Auditing: Nmap is often used by security professionals for auditing network security and identifying potential security issues.
- Network Inventory: It helps in maintaining an up-to-date inventory of network devices and services.
Nmap was named “Security Product of the Year” by Linux Journal, Info World, LinuxQuestions.Org, and Codetalker Digest. It was even featured in twelve movies, including The Matrix Reloaded, Die Hard 4, Girl With the Dragon Tattoo, and The Bourne Ultimatum.
Nmap is …
- Flexible: Supports dozens of advanced techniques for mapping out networks filled with IP filters, firewalls, routers, and other obstacles. This includes many port scanning mechanisms (both TCP & UDP), OS detection, version detection, ping sweeps, and more. See the documentation page.
- Powerful: Nmap has been used to scan huge networks of literally hundreds of thousands of machines.
- Portable: Most operating systems are supported, including Linux, Microsoft Windows, FreeBSD, OpenBSD, Solaris, IRIX, Mac OS X, HP-UX, NetBSD, Sun OS, Amiga, and more.
- Easy: While Nmap offers a rich set of advanced features for power users, you can start out as simply as “nmap -v -A targethost“. Both traditional command line and graphical (GUI) versions are available to suit your preference. Binaries are available for those who do not wish to compile Nmap from source.
- Free: The primary goals of the Nmap Project is to help make the Internet a little more secure and to provide administrators/auditors/hackers with an advanced tool for exploring their networks. Nmap is available for free download, and also comes with full source code that you may modify and redistribute under the terms of the license.
- Well Documented: Significant effort has been put into comprehensive and up-to-date man pages, whitepapers, tutorials, and even a whole book! Find them in multiple languages here.
- Supported: While Nmap comes with no warranty, it is well supported by a vibrant community of developers and users. Most of this interaction occurs on the Nmap mailing lists. Most bug reports and questions should be sent to the nmap-dev list, but only after you read the guidelines. We recommend that all users subscribe to the low-traffic nmap-hackers announcement list. You can also find Nmap on Facebook and Twitter. For real-time chat, join the #nmap channel on Freenode or EFNet.
- Acclaimed: Nmap has won numerous awards, including “Information Security Product of the Year” by Linux Journal, Info World and Codetalker Digest. It has been featured in hundreds of magazine articles, several movies, dozens of books, and one comic book series. Visit the press page for further details.
- Popular: Thousands of people download Nmap every day, and it is included with many operating systems (Redhat Linux, Debian Linux, Gentoo, FreeBSD, OpenBSD, etc). It is among the top ten (out of 30,000) programs at the Freshmeat.Net repository. This is important because it lends Nmap its vibrant development and user support communities.
Basic Nmap Commands:
Host Discovery:
nmap -sn 192.168.1.0/24This command performs a simple ping scan to discover live hosts on the network.
Port Scanning:
nmap -p 1-65535 192.168.1.1Scans all ports on a single host.
Service Version Detection:
nmap -sV 192.168.1.1Detects service versions running on the open ports.
Operating System Detection:
nmap -O 192.168.1.1Attempts to determine the operating system of the target.
Comprehensive Scan:
nmap -A 192.168.1.1Performs a comprehensive scan, including OS detection, version detection, script scanning, and traceroute.
Using Nmap Scripts:
nmap --script vuln 192.168.1.1Uses the vuln script to check for vulnerabilities.
How To Use Nmap
Nmap is pretty easy to use if you’re familiar with command-line interfaces. As it’s already installed on most Linux/Unix-based distributions, you just have to execute the ‘nmap’ command from any terminal, and that’s it. It will display several options for you.
Advanced users will also be able to use Nmap along with other system scripts and automated tasks in order to maximize the powers of this tool.
Nmap port scan command
One of the most basic Nmap commands for a scan is the nmap port scan command:
That’s how you use Nmap.
How To Install Nmap on Linux, Windows and Mac
What happens if your operating system doesn’t include Nmap? No worries, let’s see how to install it. While the installation process can differ a bit depending on the OS you are using, in most cases (MacOS and Windows) our recommendation is to get the latest release from the Nmap website’s download page.
Installing Nmap on Linux
Open the terminal and run the following commands to get Nmap installed:
- CentOS/Fedora: sudo dnf install nmap
- Ubuntu/Debian: sudo apt-get install nmap
That’s it. Nmap is now installed on Linux.
Installing Nmap on Windows
Once you download the installer, execute it and install it. The automated installer should take care of configuring Nmap for you in mere seconds.
Installing Nmap on MacOS
Mac users also have a full automated installer. Just run the Nmap-mpkg file to begin the installation. After a few seconds,
Nmap will be ready on your MacOS.
Nmap Command Examples
Let’s get to know a few useful command-line based best Nmap scans that can be performed.
1. Basic Nmap Scan against IP or host
nmap 1.1.1.1Now, if you want to scan a hostname, simply replace the IP for the host, as you see below:
nmap recordedfuture.xyzThis kind of scans, such as the Nmap scan host are perfect for your first steps when starting with Nmap.
2. Nmap Ping Scan
nmap -sp 192.168.5.0/24The most famous type of scan is the Nmap ping scan (so-called because it’s often used to perform Nmap ping sweeps), and it’s the easiest way to detect hosts on any network.
The drawback of this ICMP-only type of scan is that remote hosts often block IP-based ping packets, so if you’re unable to get solid results, we recommend switching to ARP-based requests for your scan.
3. Scan specific ports or scan entire port ranges on a local or remote server
nmap -p 1-65535 localhostIn this example, we scanned all 65535 ports for our localhost computer.
Nmap is able to scan all possible ports, but you can also scan specific ports, which will report faster results. See below:
nmap -p 80,443 8.8.8.84. Scan multiple IP addresses
Let’s try to scan multiple IP addresses. For this you need to use this syntax:
nmap 1.1.1.1 8.8.8.8You can also scan consecutive IP addresses:
nmap 1.1.1.1,2,3,4This will scan 1.1.1.1, 1.1.1.2, 1.1.1.3 and 1.1.1.4.
5. Scan IP ranges
You can also use Nmap to scan entire CIDR IP ranges, for example:
nmap 8.8.8.0/28This will scan 14 consecutive IP ranges, from 8.8.8.1 to 8.8.8.14.
An alternative is to simply use this kind of range:
nmap 8.8.8.1-14You can even use wildcards to scan the entire C class IP range, for example:
nmap 8.8.8.*This will scan 256 IP addresses from 8.8.8.1 to 8.8.8.256.
If you ever need to exclude certain IPs from the IP range scan, you can use the “–exclude” option, as you see below:
nmap -p 8.8.8.* --exclude 8.8.8.16. Scan the most popular ports
Using “–top-ports” parameter along with a specific number lets you scan the top X most common ports for that host, as we can see:
nmap --top-ports 20 192.168.1.106Replace “20” with the desired number. Output example:
[root@securitytrails:~]nmap --top-ports 20 localhost
Starting Nmap 6.40 at 2018-10-01 10:02 EDT
Nmap scan report for localhost (127.0.0.1)
Host is up (0.000016s latency).
Other addresses for localhost (not scanned): 127.0.0.1
PORT STATE SERVICE
21/tcp closed ftp
22/tcp closed ssh
23/tcp closed telnet
25/tcp closed smtp
53/tcp closed domain
80/tcp filtered http
110/tcp closed pop3
111/tcp closed rpcbind
135/tcp closed msrpc
139/tcp closed netbios-ssn
143/tcp closed imap
443/tcp filtered https
445/tcp closed microsoft-ds
993/tcp closed imaps
995/tcp closed pop3s
1723/tcp closed pptp
3306/tcp closed mysql
3389/tcp closed ms-wbt-server
5900/tcp closed vnc
8080/tcp closed http-proxy7. Scan hosts and IP addresses reading from a text file
In this case, Nmap is also useful to read files that contain hosts and IPs inside.
Let’s suppose you create a list.txt file that contains these lines inside:
192.168.1.106
recordedfuture.xyz
securitytrails.xyz
The “-iL” parameter lets you read from that file, and scan all those hosts for you:
nmap -iL list.txt8. Save your Nmap scan results to a file
On the other hand, in the following example we will not be reading from a file, but exporting/saving our results into a text file:
nmap -oN output.txt securitytrails.xyzNmap has the ability to export files into XML format as well, see the next example:
nmap -oX output.xml securitytrails.xyz9. Disabling DNS name resolution
If you need to speed up your scans a little bit, you can always choose to disable reverse DNS resolution for all your scans. Just add the “-n” parameter.
[root@securitytrails:~]nmap -p 80 -n 8.8.8.8
Starting Nmap 7.60 at 2018-10-01 09:15 -03
Nmap scan report for 8.8.8.8
Host is up (0.014s latency).
PORT STATE SERVICE
80/tcp filtered httpSee the difference with a normal DNS-resolution enabled scan:
[root@securitytrails:~]nmap -p 80 8.8.8.8
Starting Nmap 7.60 at 2018-10-01 09:15 -03
Nmap scan report for google-public-dns-a.google .com (8.8.8.8)
Host is up (0.014s latency).
PORT STATE SERVICE
80/tcp filtered http10. Scan + OS and service detection with fast execution
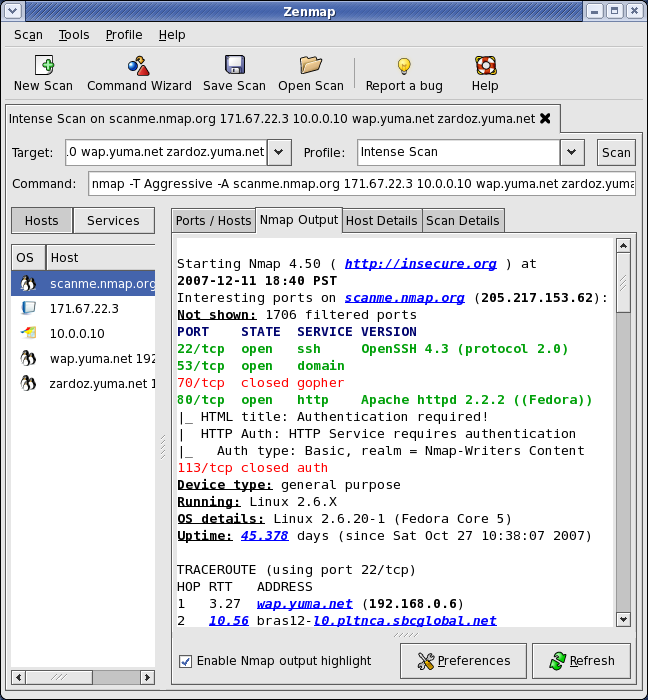
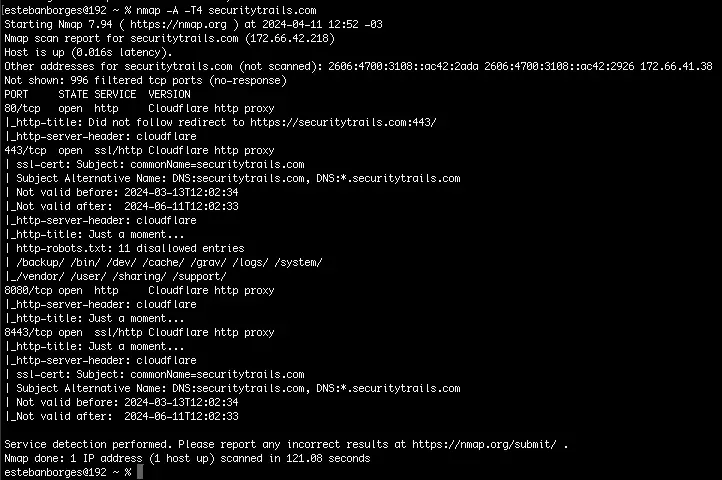
Using the “-A” parameter enables you to perform OS and service detection, and at the same time we are combining this with “-T4” for faster execution. See the example below:
nmap -A -T4 securitytrails.xyzThis is the output we got for this test:
11. Detect service/daemon versions
This can be done by using -sV parameters
nmap -sV localhostAs you can see here:
[root@securitytrails:~]nmap -sV localhost
Starting Nmap 7.60 at 2018-10-01 09:28 -03
Nmap scan report for localhost (127.0.0.1)
Host is up (0.000020s latency).
Other addresses for localhost (not scanned): ::1
Not shown: 997 closed ports
PORT STATE SERVICE VERSION
111/tcp open rpcbind 2-4 (RPC #100000)
631/tcp open ipp CUPS 2.2
902/tcp open ssl/vmware-auth VMware Authentication Daemon 1.10 (Uses VNC, SOAP)Service detection performed. Please report any incorrect results at https:// nmap .org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 7.96 seconds
12. Scan using TCP or UDP protocols
One of the things we love most about Nmap is the fact that it works for both TCP and UDP protocols. And while most services run on TCP, you can also get a great advantage by scanning UDP-based services. Let’s see some examples.
Standard TCP scanning output:
[root@securitytrails:~]nmap -sT 192.168.1.1Starting Nmap 7.60 at 2018-10-01 09:33 -03
Nmap scan report for 192.168.1.1
Host is up (0.58s latency).
Not shown: 995 closed ports
PORT STATE SERVICE
80/tcp open http
1900/tcp open upnp
20005/tcp open btx
49152/tcp open unknown
49153/tcp open unknown
Nmap done: 1 IP address (1 host up) scanned in 1.43 secondsUDP scanning results using “-sU” parameter:
[root@securitytrails:~]nmap -sU localhost
Starting Nmap 7.60 at 2018-10-01 09:37 -03
Nmap scan report for localhost (127.0.0.1)
Host is up (0.000021s latency).
Other addresses for localhost (not scanned): ::1
Not shown: 997 closed ports
PORT STATE SERVICE
68/udp open|filtered dhcpc
111/udp open rpcbind
5353/udp open|filtered zeroconf13. CVE detection using Nmap
One of Nmap’s greatest features that not all the network and systems administrators know about is something called “Nmap Scripting Engine” (known as NSE). This scripting engine allows users to use a pre-defined set of scripts, or write their own using Lua programming language.
Using Nmap scripts is crucial in order to automate system and vulnerability scans. For example, if you want to run a full vulnerability test against your target, you can use these parameters:
nmap -Pn --script vuln 192.168.1.105Output example:
[root@securitytrails:~]nmap -Pn --script vuln 192.168.1.105
Starting Nmap 7.60 at 2018-10-01 09:46 -03
Pre-scan script results:
| broadcast-avahi-dos:
| Discovered hosts:
| 224.0.0.251
| After NULL UDP avahi packet DoS (CVE-2011-1002).
|_ Hosts are all up (not vulnerable).
Nmap scan report for 192.168.1.105
Host is up (0.00032s latency).
Not shown: 995 closed ports
PORT STATE SERVICE
80/tcp open http
|_http-csrf: Couldn't find any CSRF vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server open and hold
| them open as long as possible. It accomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, it starves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
|_ https:// cve.mitre .org/cgi-bin/cvename.cgi?name=CVE-2007-6750
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-vuln-cve2014-3704: ERROR: Script execution failed (use -d to debug)
1900/tcp open upnp
20005/tcp open btx
49152/tcp open unknown
49153/tcp open unknownAs you can see, in this vulnerability test we were able to detect one CVE (Slowloris DOS attack).
14. Flood testing with Nmap
Nmap features never seem to end, and thanks to the NSE, that even allows us to launch flood attacks against our network to test how effective our mitigation methods are.
In our previous example (#12) we found the host was vulnerable to Slowloris attack, and now we’ll try to exploit that vulnerability by launching a flood attack in a forever loop:
nmap 192.168.1.105 -max-parallelism 800 -Pn --script http-slowloris --script-args http-slowloris.runforever=true15. Testing brute force attacks
NSE is really fascinating — it contains scripts for everything you can imagine. See the next three examples of BFA against WordPress, MSSQL, and FTP server:
nmap -sV –script http-wordpress-brute –script-args ‘userdb=users.txt,passdb=passwds.txt,http-wordpress-brute.hostname=domain.xyz, http-wordpress-brute.threads=3,brute.firstonly=true’ 192.168.1.105
WordPress brute force attack:
nmap -p 1433 --script ms-sql-brute --script-args userdb=customuser.txt,passdb=custompass.txt 192.168.1.105Brute force attack against MS-SQL:
nmap -p 1433 --script ms-sql-brute --script-args userdb=customuser.txt,passdb=custompass.txt 192.168.1.105FTP brute force attack:
nmap --script ftp-brute -p 21 192.168.1.10516. Detecting malware infections on remote hosts
Nmap is able to detect malware and backdoors by running extensive tests on a few popular OS services like Identd, Proftpd, Vsftpd, IRC, SMB, and SMTP. It also has a module to check for popular malware signs inside remote servers and integrates Google’s Safe Browsing and VirusTotal databases as well.
A common malware scan can be performed by using:
nmap -sV --script=http-malware-host 192.168.1.105Or using Google’s Malware check:
nmap -p80 --script http-google-malware infectedsite.xyzOutput example:
Nmap is one of the most complete and accurate port scanners used by infosec professionals today. With it, you can perform simple port scan tasks or use its powerful scripting engine to launch DOS attacks, detect malware or brute force testing on remote and local servers.
Today we covered the top fifteen Nmap commands to scan remote hosts, but there’s a lot more to discover if you’re starting to use Nmap in your OSINT strategy.
Nmap has been one of the most popular port and network scanners for decades. Still, new users often have questions about how it works and its legal usage, and even look for other, similar software from time to time.
Is Nmap free?
Yes, Nmap is completely free for you to download and use. It’s also an open source (licensed) project, so you can inspect, modify, and enhance it to match your needs.
Is Nmap Legal?
Nmap is legal; however, that hinges entirely on the purpose the user has for using it. Scanning your own network is totally legal, but scanning third-party networks may get you into legal problems if you aren’t authorized, depending on the country and state in which you live.